In many projects, cybersecurity is still viewed as only becoming relevant at the end of the development process in the form of tests, audits, or security measures. However, this understanding is incomplete. In modern software and system development, security vulnerabilities can arise as early as the conceptualization and design phases. Those who take cybersecurity seriously must therefore view it as an integral part of the entire development process.
At its core, cybersecurity in development means considering security aspects from the beginning. According to the “Security by Design” principle, security is embedded in the system as a fixed feature from the start, rather than being “added on” later. This includes defining security requirements, systematically identifying potential vulnerabilities, and conducting structured risk assessments. The goal is to prevent vulnerabilities from arising in the first place rather than having to fix them later.
Why Early Risk Detection Is Critical
The timing of identifying security issues is critical. The earlier they are identified, the easier and more cost-effective it is to resolve them. While errors in the early stages of development can often be corrected with minimal effort, security vulnerabilities that arise during later operations frequently result in significant financial, legal, and reputational damage.
The “Security by Design” concept aims to embed security as an integral part of development from the beginning, rather than adding it as an afterthought. With this approach, security requirements, potential threats, and possible vulnerabilities are considered as early as the planning phase. The result is systems with security mechanisms built in from the start rather than having to react to incidents or vulnerabilities afterward.
This approach reduces risks and associated costs, supports compliance with regulatory requirements, and improves the long-term quality and maintainability of systems. Methods that enable early risk detection and systematically integrate security aspects into the development process are therefore of critical importance.
Threat Modeling: Systematically Identifying Risks
In this context, threat modeling is a key method. It provides a practical toolkit for implementing security by design. Threat modeling is a structured approach used to identify and analyze potential threats to a system before it is implemented.
Three fundamental questions are at the heart of this process: What needs to be protected? What must it be protected from? And how critical are the respective risks? First, the relevant data, functions, and interfaces of a system are identified to answer these questions. Then, potential threats, such as unauthorized access, manipulation, or system failures, are analyzed. Then, an assessment of vulnerabilities and risks is conducted. Ultimately, this assessment leads to the development of concrete security objectives and appropriate measures.
TARA: Structured Risk Analysis in Practice
TARA (Threat Analysis and Risk Assessment) is a well-established, concrete threat modeling methodology used across many industries. It provides a clearly defined framework for identifying and assessing cybersecurity risks, as well as deriving appropriate countermeasures, in a systematic manner.
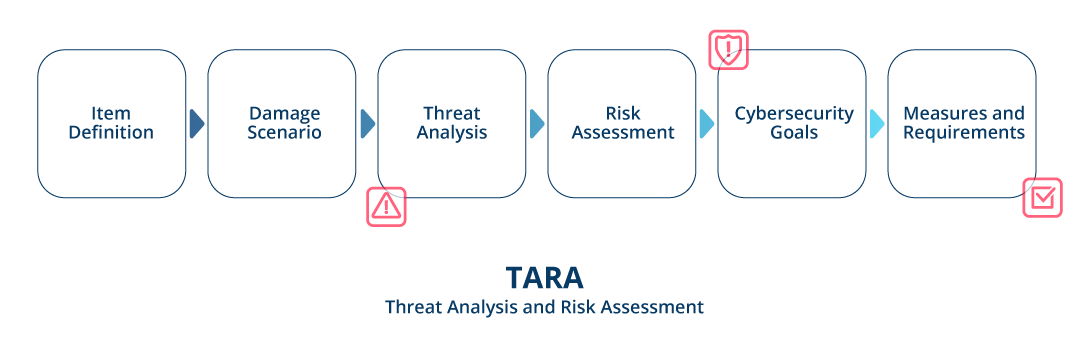
The TARA approach typically follows a logical sequence.
First, the system is identified and analyzed in context. This involves determining which functions, components, interfaces, and operating environments to examine. Based on this analysis, a potential damage impact analysis is conducted. This involves assessing the consequences of successful attacks on functional safety, data protection, financial assets, and system operation.
Next, specific threat scenarios are identified. This involves examining the attack vectors through which the system could be compromised and the vulnerabilities that potential attackers could exploit. These insights are then incorporated into the risk assessment. Factors such as the feasibility of an attack and the potential extent of damage are combined to prioritize risks.
This assessment ultimately defines cybersecurity objectives, as well as specific measures and requirements for development. The goal is to proactively avoid, reduce, or manage risks.
TARA’s major advantage lies in its clear structure and traceability. Decisions are documented and can be reviewed at any time, which is particularly critical in regulated sectors such as the automotive industry (e.g., in the context of ISO/SAE 21434).
From Intuition to Methodology
Many teams already consider security, though often implicitly or based on experience. With Security by Design and Threat Modeling, however, decisions are grounded in a structured analysis rather than made based on gut instinct.
This methodical approach is becoming increasingly important, particularly in regulated industries. Methods such as threat analysis and risk assessment (TARA) demonstrate how security requirements can be derived and integrated into development processes systematically.
Cybersecurity as an End-to-End Process
In practice, people often mistakenly view security analyses as a one-time task. However, in reality, cybersecurity—in the sense of “security by design”—is not an isolated step. Rather, it is an end-to-end process that accompanies all phases of development, from requirements and architecture to implementation, testing, and validation.
A resilient and long-term secure system can only be created when security aspects are continuously taken into account.
Conclusion
Cybersecurity in development doesn’t necessarily mean more work. Rather, it means making better decisions at the right time. Security by Design provides the strategic framework, and methods such as threat modeling—particularly TARA—enable operational implementation.
If you’re ready to see how cybersecurity works in practice, check out the webinar „Cybersecurity in development“. It’s a great opportunity to understand the concepts described in this article in a concrete application context.

